Some Known Details About Risk Management Enterprise
Table of ContentsRisk Management Enterprise Can Be Fun For AnyoneThe smart Trick of Risk Management Enterprise That Nobody is DiscussingThe Of Risk Management EnterpriseThe Ultimate Guide To Risk Management EnterpriseRisk Management Enterprise for BeginnersThe Definitive Guide to Risk Management EnterpriseSome Known Facts About Risk Management Enterprise.
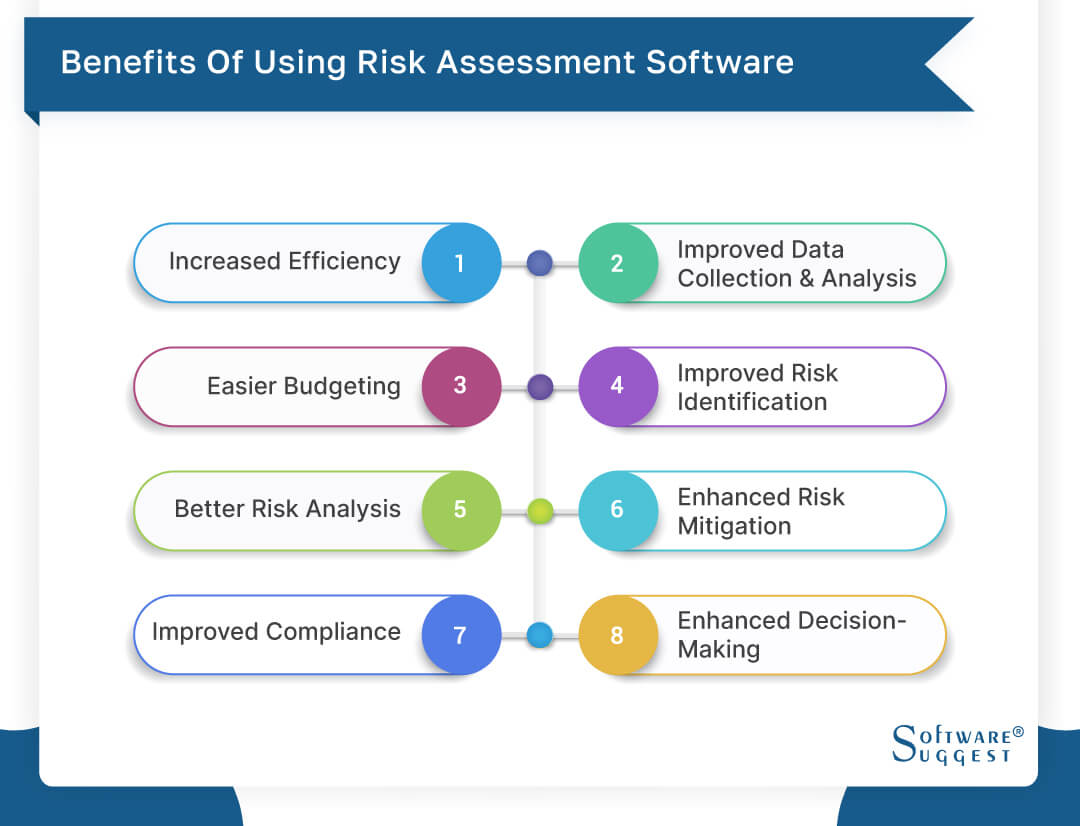
Below are some of its crucial functions that facilities must understand. So, have a look. Real-Time Risk Assessments and Reduction in this software application enable organizations to continuously monitor and evaluate risks as they evolve. This feature leverages real-time information and computerized evaluation to recognize potential risks without delay. As soon as threats are recognized, the software program helps with immediate reduction activities.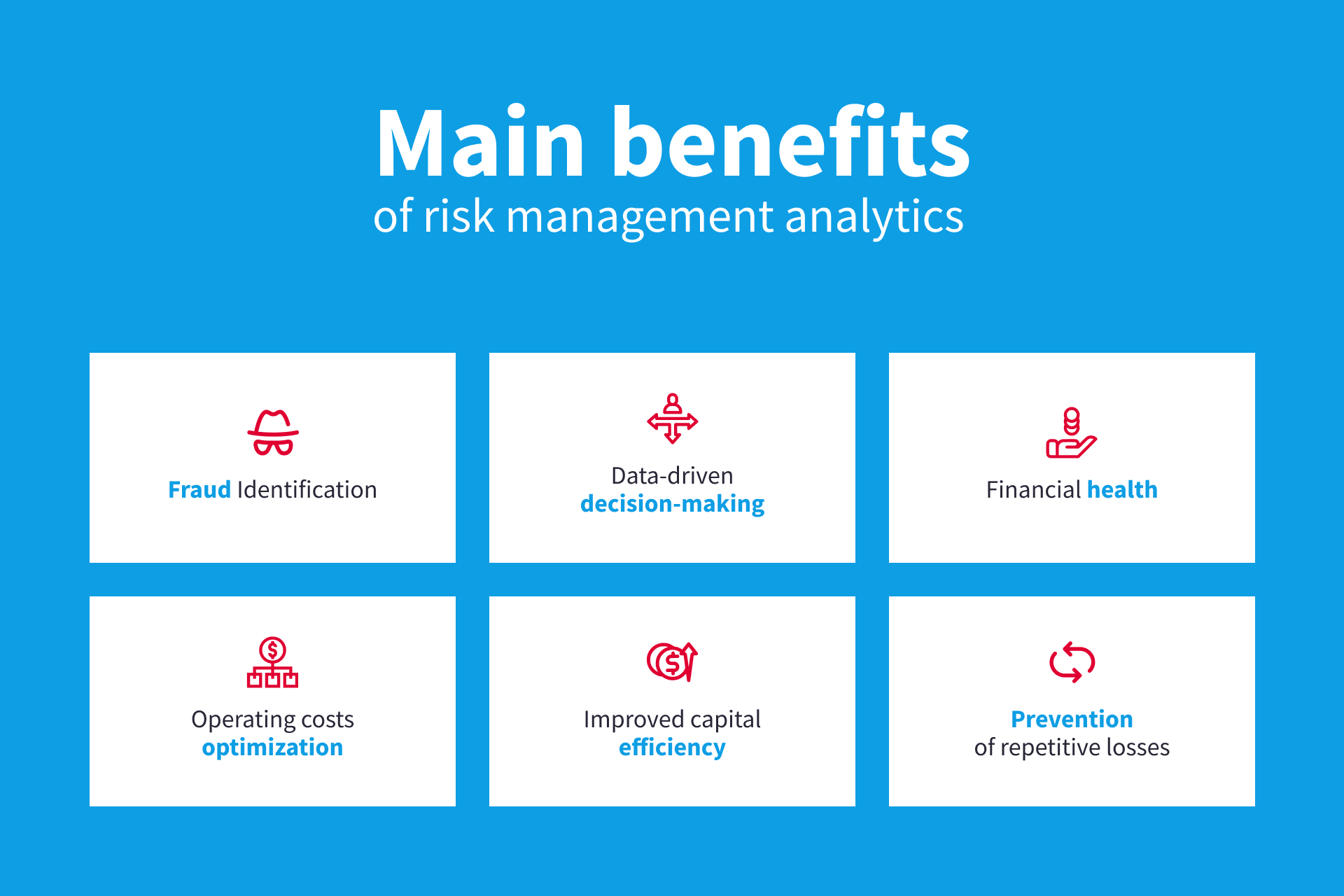
They resolve the challenge of continuous threat administration by offering devices to check threats constantly. KRIs enhance safety and security risk oversight, making certain that prospective threats are identified and taken care of successfully.
How Risk Management Enterprise can Save You Time, Stress, and Money.
IT risk administration is a subset of business danger administration (ERM), made to bring IT run the risk of in line with an organization's risk cravings. IT run the risk of monitoring (ITRM) includes the plans, treatments and innovation necessary to minimize risks and susceptabilities, while maintaining conformity with suitable regulative demands. Furthermore, ITRM seeks to limit the effects of destructive occasions, such as safety and security breaches.
Veronica Rose, ISACA board supervisor and a details systems auditor at Metropol Corp. The ISACA Threat IT framework straightens well with the COBIT 2019 framework, Rose claimed.
Business Risk Administration Software Development: Conveniences & Features, Cost. With technical advancements, threats are continuously on the surge., services navigate with a frequently transforming sea of risks.
Some Known Questions About Risk Management Enterprise.
In this blog, we will study the world of ERM software, exploring what it is, its benefits, attributes, and so on to ensure that you can build one for your business. Business Threat Administration (ERM) software program is the application program for planning, directing, organizing, and managing service tasks and improving risk administration procedures.
With ERM, organizations can make insightful choices to enhance the general strength of business. Read: ERP Application Advancement Committed ERM systems are critical for organizations that regularly manage large quantities of sensitive information and multiple stakeholders to authorize calculated choices. Some markets where ERM has actually come to be a conventional system are health care, money, building and construction, insurance coverage, and infotech (IT).
It can be stayed clear of by making use of the ERM software application system. This system automates guideline compliance monitoring to maintain the organization secure and certified.
Risk Management Enterprise - Truths
You can likewise attach existing software application systems to the ERM by means of APIs or by adding information manually. Organizations can utilize ERM to assess threats based upon their possible impact for much better threat monitoring and mitigation.: Including this function allows customers to get real-time notices on their devices about any type of danger that may occur and its effect.
Instead, the software program allows them to establish limits for different procedures and send push alerts in situation of feasible threats.: By integrating data visualization and reporting in the personalized ERM software program, companies can acquire clear insights regarding threat patterns and performance.: It is compulsory for companies to you could try here abide by market conformity and regulative criteria.
These platforms make it possible for companies to implement best-practice danger monitoring procedures that straighten with market standards, supplying an effective, technology-driven method to determining, assessing, and mitigating risks. This blog discovers the advantages of computerized risk administration devices, the areas of risk monitoring they can automate, and the value they give an organization.
The 2-Minute Rule for Risk Management Enterprise
Teams can establish kinds with the pertinent fields and quickly develop different forms for various danger types. These threat analysis kinds can be distributed for completion using automated workflows that send notifications to the pertinent internet personnel to finish the kinds online. If types are not completed by the due date, after that chaser emails are instantly sent out by the system.
The control monitoring and control testing procedure can also be automated. Firms can use computerized process to send out normal control examination notices and team can go into the results by means of on-line kinds. Controls can additionally be checked by the software application by establishing guidelines to send out alerts based upon control information held in other systems and spread sheets that is drawn into the system through API assimilations.
Threat management automation software application can likewise sustain with danger coverage for all degrees of the venture. Leaders can see reports on danger exposure and control performance via a variety of reporting outcomes including fixed reports, Power BI interactive reports, bowtie analysis, and Monte Carlo simulations. The ability to draw genuine time records at the touch of a switch removes difficult information manipulation jobs leaving risk teams with even more time to evaluate the information and encourage the company on the most effective strategy.
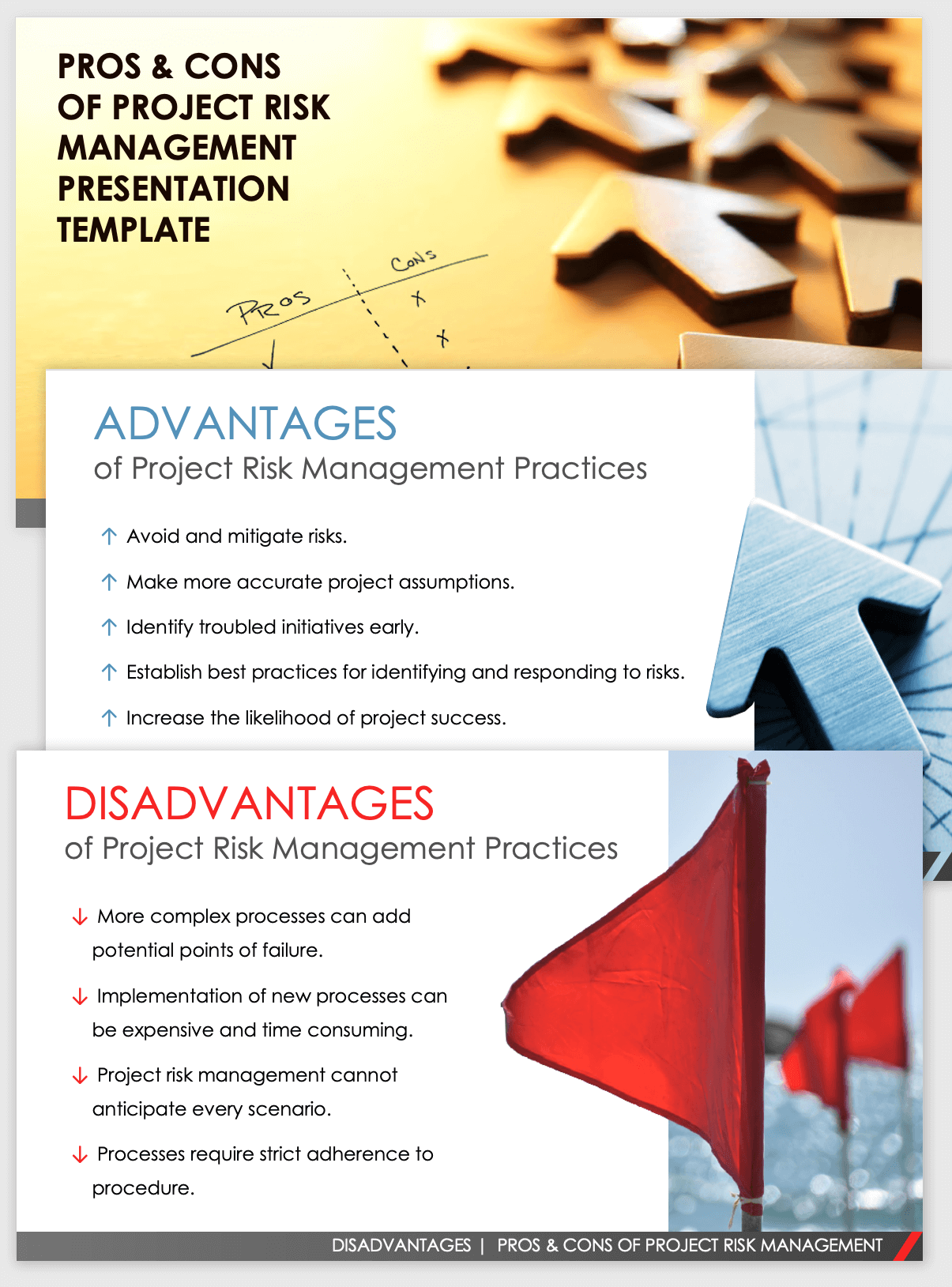
Organizations operating in affordable, fast-changing markets can't afford delays or inadequacies in dealing with possible dangers. Typical threat administration using manual spreadsheet-based procedures, while familiar, frequently lead to fragmented information, lengthy reporting, and an enhanced possibility of human mistake.
Getting My Risk Management Enterprise To Work
This makes sure danger registers are constantly existing and lined up look at this web-site with organizational goals. Conformity is an additional vital vehicle driver for automating risk monitoring. Criteria like ISO 31000, CPS 230 and COSO all give assistance around danger management finest methods and control frameworks, and automated threat monitoring devices are structured to align with these needs helping firms to fulfill most generally utilized danger administration requirements.
Seek risk software program systems with an approvals pecking order to quickly establish operations for danger acceleration. This functionality enables you to customize the view for each individual, so they only see the data appropriate to them. Ensure the ERM software offers individual tracking so you can see that entered what data and when.
Look for out tools that provide job danger monitoring abilities to manage your tasks and profiles and the connected dangers. The benefits of taking on threat monitoring automation software program extend much past performance.
The 4-Minute Rule for Risk Management Enterprise
While the situation for automation is compelling, implementing a threat monitoring system is not without its difficulties. For one, data top quality is vital. Automated systems rely upon accurate, current information to supply meaningful insights. To overcome the challenges of risk monitoring automation, organizations should buy information cleansing and administration to ensure a solid structure for applying an automated system.
Automation in threat management empowers businesses to change their approach to run the risk of and develop a more powerful foundation for the future (Risk Management Enterprise). The concern is no much longer whether to automate danger administration, it's exactly how quickly you can start. To see the Riskonnect in action,
The response typically depends on how well threats are expected and managed. Job management software program offers as the navigator in the tumultuous waters of job implementation, offering tools that recognize and evaluate threats and create methods to minimize them successfully. From real-time information analytics to thorough risk surveillance dashboards, these devices supply a 360-degree view of the task landscape, allowing job managers to make informed decisions that maintain their tasks on course and within budget.